 For years, those of us who dared to talk about NSA domestic spying were labeled complete “kooks” by the mainstream media. A few months ago, however, we learned that the NSA is listening in on nearly everything we do online, and had been for years!
For years, those of us who dared to talk about NSA domestic spying were labeled complete “kooks” by the mainstream media. A few months ago, however, we learned that the NSA is listening in on nearly everything we do online, and had been for years!
And they’re by no means the only ones working night and day to breech your privacy…
The most clear and present danger to most of us isn’t the FBI, NSA, or even the KGB… it’s fraudsters, hackers, and identity thieves.
But here’s the good news, you can protect against all threats at the same time, using the same simple methods, five of which I share in this post. Of course, there are dozens more ways to safeguard your privacy.
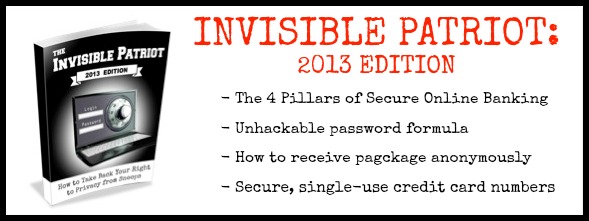
Last week, I published an entire report about how to get your identity off the control grid. It’s a mixture of common sense identity protection skills and secret agent tactics that will make you invisible to fraudsters, hackers, and even government agencies…
I recommend taking these 5 steps today:
1. Activate all protection systems.
Many operating systems come with a built-in firewall, spam blocker, anti-virus software, or other security applications. Be sure these are activated. Your Internet service provider may provide an e-mail spam filtering service that should also be turned on.
2. Update your protection.
Most people don’t do this. They have a 2-year-old version of a virus scanner and they think they’re 100% protected. Using security software won’t help if it’s not up to date. Be sure that you are using the latest versions of spam, spyware and virus-detection software.
3. Install a security toolbar.
Browser toolbars with security features offer an additional line of defense against malware and spyware. Most include features that block pop-ups, spam and known phishing sites. Some are even able to detect potential consumer scams.
4. Create user accounts for day-t0-day activities.
Whether you use Windows or Mac, you can create user accounts that are separate from the default administrator account for your operating system. Users accounts are fine for most everyday purposes. Only log in as the administrator when making configuration changes to the computer. When the administrator account is used infrequently, the access to change configurations will be more limited to hacking.
You may also want to create an individual user account for each member of the family who uses the computer. This will allow for each person to keep his or her information private.
5. Turn off your computer.
A lot of us make this mistake. When you are not actively using your computer, shut down or disconnect from the Internet. If your computer is on-line less frequently, the chance of access by a malicious source decreases.

Great article! Thank you for posting!
This is a good articular like the others. I have some of the others but my financial situation is not cooperating with the items I would like to have and read. then find out what I can do and then can’t do! Thank you for all of the different books and other informational readings!
Bruce Hartog
Wildwood, FL 34785
thank you all of this is good to know